How to get in-app purchases for free in Android
In this post i will teach you how to get in-app purchases for free in Android device. There are paid apps, that you need to pay before you download it. But there are apps which is free to download, but in game there are some things that you can buy with real money, or activate to Pro version. And in this post we gonna learn to do that all for free.
1) You need a rooted Android device.
2) Download this app and install it.
3) Now go to Settings of your device. And from Security select Unknown sources.
4) After that you need to change time zone of phone to the Moscow GMT +4:00.
5) After that open app you just downloaded on step 2. And you need to press on the Grant button from pop out SuperSU window. And your device need to be connected to the internet!
6) And you can see the list of your apps, where in-app purchase is available.
7) Choose one app from list and wait after its finished loading.
8) And after app opened, you need to go to page of upgrading, or if its a game the press on the plus button to buy coins or something like that.
9) After that press on the purchase button and in pop out little window press on BUY button.
10) And You can see Payment Successful message.
11) But after you finished in-app purchasing i recommend you to delete that app, if you want to do in-app purchasing then install it again.
12) Now you can't use Play Store, its showing no connection error message.
13) After you have deleted that app, you need to install one app from this post. Do all as in that post and open that hosts file.
14) And remove 2nd line from file. Only keep first line 127.0.0.1 localhost and press on the save button and in pop out window press on the OK button and after that on Yes button.
And that's all. You can ope Play Store!
Hackers Dictionary
If you are a newbie in hacking then you need to learn some things. There are some terms that every hacker should know about them. Some words and abbreviations that you should know.
Some words you need to know aboutAlgorithm - A series of steps specifying which actions to take in which order.
ANSI Bomb - ANSI.SYS key-remapping commands consist of cryptic-looking text that specifies, using ansi numeric codes to redefine keys.
Back Door - Something a hacker leaves behind on a system in order to be able to get back in at a later time.
Binary - A numbering system in which there are only two possible values for each digit: 0 and 1.
Black Hat - A hacker who performs illegal actions to do with hacking online. (Bad guy, per se)
Blue Hat - A blue hat hacker is someone outside computer security consulting firms who is used to bug test a system prior to its launch, looking for exploits so they can be closed. Microsoft also uses the term BlueHat to represent a series of security briefing events.
Bot - A piece of malware that connects computer to an attacker commonly using the HTTP or IRC protocal to await malicous instructions.
Botnet - Computers infected by worms or Trojans and taken over by hackers and brought into networks to send spam, more viruses, or launch denial of service attacks.
Buffer Overflow - A classic exploit that sends more data than a programmer expects to receive. Buffer overflows are one of the most common programming errors, and the ones most likely to slip through quality assurance testing.
Cracker - A specific type of hacker who decrypts passwords or breaks software copy protection schemes.
DDoS - Distributed denial of service. Flooding someones connection with packets. Servers or web-hosted shells can send packets to a connection on a website usually from a booter.
Deface - A website deface is an attack on a site that changes the appearance of the site or a certain webpage on the site.
Dictionary Attack - A dictionary attack is an attack in which a cyber criminal can attempt to gain your account password. The attack uses a dictionary file, a simple list of possible passwords, and a program which fills them in. The program just fills in every single possible password on the list, untill it has found the correct one. Dictionary files usually contain the most common used passwords.
DOX - Personal information about someone on the Internet usualy contains real name, address, phone number, SSN, credit card number, etc.
E-Whore - A person who manipulates other people to believe that he/she is a beautiful girl doing cam shows or selling sexual pictures to make money.
Encryption - In cryptography, encryption applies mathematical operations to data in order to render it incomprehensible. The only way to read the data is apply the reverse mathematical operations. In technical speak, encryption is applies mathematical algorithms with a key that converts plaintext to ciphertext. Only someone in possession of the key can decrypt the message.
Exploit - A way of breaking into a system. An exploit takes advantage of a weakness in a system in order to hack it.
FUD - Fully undetectable, can be used in many terms. Generally in combination with crypters, or when trying to infect someone.
Grey Hat - A grey hat hacker is a combination of a Black Hat and a White Hat Hacker. A Grey Hat Hacker may surf the internet and hack into a computer system for the sole purpose of notifying the administrator that their system has been hacked, for example. Then they may offer to repair their system for a small fee.Hacker (definition is widely disputed among people...) = A hacker is someone who is able to manipulate the inner workings of computers, information, and technology to work in his/her favor.
Hacktivist - A hacktivist is a hacker who utilizes technology to announce a social, ideological, religious, or political message. In general, most hacktivism involves website defacement or denial-of-service attacks.
IP Address - On the Internet, your IP address is the unique number that others use to send you traffic.
IP Grabber - A link that grabs someone's IP when they visit it. Keylogger - A software program that records all keystrokes on a computer's keyboard, used as a surveillance tool or covertly as spyware.Leach = A cultural term in the warez community referring to people who download lots of stuff but never give back to the community.
LOIC/HOIC - Tool(s) used by many anonymous members to conduct DDoS attacks. It is not recommended to use these under any circumstances.
Malware - Software designed to do all kinds of evil stuff like stealing identity information, running DDoS attacks, or soliciting money from the slave. Neophyte = A neophyte, "n00b", or "newbie" is someone who is new to hacking or phreaking and has almost no knowledge or experience of the workings of technology, and hacking.
smith - Somebody new to a forum/game.
OldFag - Somebody who's been around a forum/game for a long time.
Packet - Data that is sent across the Internet is broken up into packets, sent individually across the network, and reassembled back into the original data at the other end.
Phreak - Phone Freaks. Hackers who hack cell phones for free calling. Free Long distance calling. Etc.
Phreaking - The art and science of cracking the phone network. Proxy - A proxy is something that acts as a server, but when given requests from clients, acts itself as a client to the real servers. Rainbow Table - A rainbow table is a table of possible passwords and their hashes. It is way faster to crack a password using rainbow tables then using a dictionary attack (Bruteforce).
Remote Administration Tool - A tool which is used to remotely control (an)other machine(s). These can be used for monitoring user actions, but often misused by cyber criminals as malware, to get their hands on valuable information, such as log in credentials. Resolver - Software created to get an IP address through IM (instant messenger, like Skype/MSN) programs.
Reverse Engineering - A technique whereby the hacker attempts to discover secrets about a program. Often used by crackers, and in direct modifications to a process/application.
Root - Highest permission level on a computer, able to modify anything on the system without restriction.
Rootkit (ring3 ring0) - A powerful exploit used by malware to conceal all traces that it exists. Ring3 - Can be removed easily without booting in safemode. Ring0 - Very hard to remove and very rare in the wild, these can require you to format, it's very hard to remove certain ring0 rootkits without safemode.
Script Kiddie - A script kid, or skid is a term used to describe those who use scripts created by others to hack computer systems and websites. Used as an insult, meaning that they know nothing about hacking.
Shell - The common meaning here is a hacked web server with a DoS script uploaded to conduct DDoS attacks via a booter. OR A shell is an script-executing unit - Something you'd stick somewhere in order to execute commands of your choice.
Social Engineer - Social engineering is a form of hacking that targets people's minds rather than their computers. A typical example is sending out snail mail marketing materials with the words "You may already have won" emblazoned across the outside of the letter. As you can see, social engineering is not unique to hackers; it's main practitioners are the marketing departments of corporations.
Spoof - The word spoof generally means the act of forging your identity. More specifically, it refers to forging the sender's IP address (IP spoofing). (Spoofing an extension for a RAT to change it from .exe to .jpg, etc.)
SQL Injection - An SQL injection is a method often used to hack SQL databases via a website, and gain admin control (sometimes) of the site. You can attack programs with SQLi too.
Trojan - A Trojan is a type of malware that masquerades as a legitimate file or helpful program with the ultimate purpose of granting a hacker unauthorized access to a computer.
VPS - The term is used for emphasizing that the virtual machine, although running in software on the same physical computer as other customers' virtual machines, is in many respects functionallyequivalent to a separate physical computer, is dedicated to the individual customer's needs, has the privacy of a separate physical computer, and can be configured to run server software. Warez - Software piracy
White Hat - A "white hat" refers to an ethical hacker, or a computer security expert, who specializes in penetration testing and in other testing methods to ensure the security of a businesses information systems. (Good guy, per se)
Worm - Software designed to spread malware with little to no human interaction. Zero Day Exploit = An attack that exploits a previously unknown vulnerability in a computer application, meaning that the attack occurs on "day zero" of awareness of the vulnerability. This means that the developers have had zero days to address and patch the vulnerability.
AbbreviationsDDoS - Distributed Denial of Service
DrDoS - Distributed Reflected Denial of Service Attack, uses a list of reflection servers or other methods such as DNS to spoof an attack to look like it's coming from multiple ips. Amplification of power in the attack COULD occur.
FTP - File Transfer Protocol. Used for transferring files over an FTP server.
FUD - Fully Undetectable
Hex - In computer science, hexadecimal refers to base-16 numbers. These are numbers that use digits in the range: 0123456789ABCDEF. In the C programming language (as well as Java, JavaScript, C++, and other places), hexadecimal numbers are prefixed by a 0x. In this manner, one can tell that the number 0x80 is equivalent to 128 decimal, not 80 decimal.
HTTP - Hyper Text Transfer Protocol. The foundation of data communication for the World Wide Web.
IRC - Internet Relay Chat. Transmiting text messages in real time between online users.
JDB - Java drive-by, a very commonly used web-based exploit which allows an attacker to download and execute malicious code locally on a slave's machine through a widely known java vulnerability.
Malware - Malicious Software
Nix - Unix based operating system, usually refered to here when refering to DoS'ing.
POP3 - This is the most popular protocol for picking up e-mail from a server.
R.A.T - Remote Administration Tool
SDB - Silent drive-by, using a zero day web-based exploit to hiddenly and un-detectably download and execute malicious code on a slave's system. (similar to a JDB however no notification or warning is given to the user)
SE - Social Engineering
Skid - Script Kid/Script Kiddie
SMTP - A TCP/IP protocol used in sending and receiving e-mail. SQL - Structured Query Language. It's a programming language, that used to communicate with databases and DBMS. Can go along with a word after it, such as "SQL Injection."
SSH - Secure Shell, used to connect to Virtual Private Servers.
TCP - Transmission Control Protocol, creates connections and exchanges packets of data.
UDP - User Datagram Protocol, An alternative data transport to TCP used for DNS, Voice over IP, and file sharing.
VPN - Virtual Private Network
VPS - Virtual Private Server
XSS (CSS) - Cross Site Scripting
You should learn this all. Else you will stay a newbie.
Change Processor Name Permanently
There are a way to change your computer CPU name from Properties of it. So you can prank with friends with this trick. Change the name to whatever you want and make a dream computer for your friends. No need to download any software, we can do that all without any third party software.
1) Open notepad and type in text given below.
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\CentralProcessor\0] "ProcessorNameString"="Intel(R) Core(TM) i7-2600K CPU @ 6.60GHz"You can change Intel(R) Core(TM) i7-2600K CPU @ 6.60GHz to whatever you want.
2) Save file as processor.reg.
3) Now open it, and after that in pop out warn windows press on the Yes button and after that on OK button to close it.
4) Now go to properties of your computer and you can see the results!
Speed Up Internet Connection using DNS
In previous post i posted the best solutions to speed up your internet connection. And visitors find it useful and post helped them a lot. So in this post i will show you another way to speed up internet connection using DNS.
1. Right click on small network icon at bottom of right side and select Open network and sharing center.
2. Select network connection and press on the Properties button in new opened small window.
3. Switch to the Networking tab and double click on Internet Protocol Version 4 (TCP/IPv4). Tick on Use the following DNS server addresses and fill the Preferred DNS server and Alternate DNS server with any values of given below.
Google DNS
Preferred DNS server: 8.8.8.8
Alternate DNS server: 8.8.4.4
Open DNS
Preferred DNS server: 208.67.222.222
Alternate DNS server: 208.67.220.220
4. After that click on OK button and its better to restart computer.
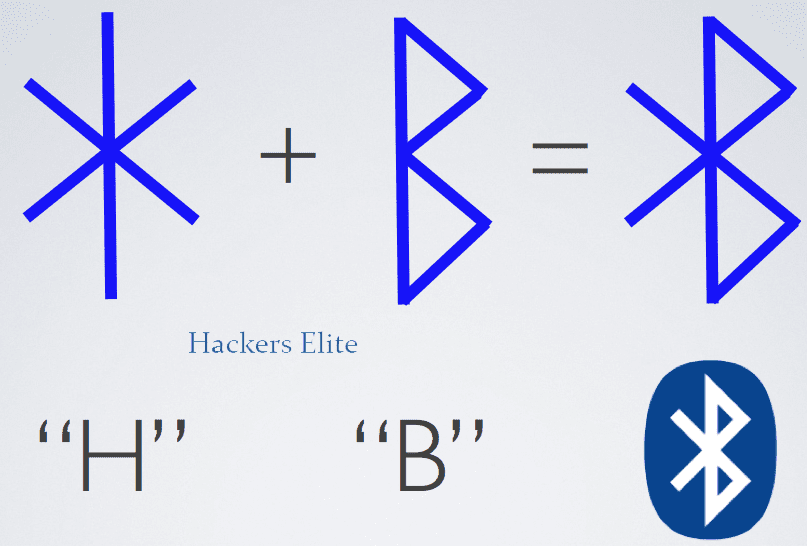
The Bluetooth History and Name
Nowadays anybody know about Bluetooth. But i think after some years it will be out of date, because NFC comes to change it. But still Bluetooth is really important part of our device. So ever you interested about Bluetooth, why its called Bluetooth? The story of Bluetooth. If no then you should read this post, because its and informative and interesting.
Intel mobile computing engineer Jim Kardach was approached by his boss him asking him to develop technology which would help integrate wireless into the notebook. Jim developed a technology for exchanging data over short distances using short-wavelength radio transmissions.
Intel later approached a small group of companies including Ericsson and Nokia, IBM, Motorola, Nokia and Toshiba to form a consortium to discuss the short range wireless technologies and the need to develop a single short-range standard for the same. The idea was to discourage having three or more competing standards for the same technology. During this process of negotiations, it was noticed that each company referred to the technology by different names and this created much confusion. It was then that Jim came up with a code name Bluetooth. Jim Kardach being a huge history fan heard from Sven of Ericson talk about a 10th century king of Denmark. Back at home he received a novel he had ordered named ‘The Vikings’ by Gwyn in which he again read about the Harald Balaatand whom Sven had mentioned. King Harald Blaatand “Bluetooth” 11 united parts of Norway and the dissonant Danish tribes into a single kingdom and ruled Denmark and Sweden seamlessly. Jim proposed the codename to the Special Interest Group (SIG) that was working on a single standard. Harold “Bluetooth’s” success in uniting Scandinavia seemed like the perfect name to describe a technology which would make PC’s and phones communicate seamlessly. This name was initially proposed as a codename only until the group came up with a singular name for the technology. However, the group evidently adopted the name in the end.
That's all you need to know about Bluetooth. I hope you find this interesting. Then make sure you share this post with your friends.
Soccer World Cup related Websites Hacked
Anonymous promised cyber-attack on World Cup Sponsors. They kicked offline earlier this week include World Cup sponsor Hyundai and government state Mato Grosso.
"We had a busy last few days and there is more still to come," a hacker who calls himself Che Commodore and who claims to be a member of the Anonymous hacker collective told Reuters on Wednesday.
"Companies and institutions that work with a government that denies the basic rights of its people in order to promote a private, exclusive and corrupt sports event will be targeted"
"Cyberattacks have become a popular way of gaining notoriety and publicity, though it’s not clear what motivations were behind this attack but could well be the issues that have seen Brazilians protesting almost daily," Edward Parsons, senior manager in the cyber security at KPMG, said in an emailed statement to Mashable.
They are using DDos ( Distributed Denial of Service ) to destroy websites.
Hackers broke into the foreign ministry's email service, accessing dozens of classified documents including a list of foreign dignitaries planning to attend World Cup matches.
Group of Hackers Anonymous plan Cyber-Attack on World Cup Sponsors
Group of Hackers Anonymous plan cyber-attack on FIFA world cup 2014 sponsors. As they say meaning of this cyber attack is to protest the lavish spending on the soccer games in a country struggling to provide basic services.
“We have a plan of attack,” Commodore told the agency “We have already conducted late-night tests to see which of the sites are more vulnerable… This time we are targeting the sponsors of the World Cup.”
"This time we are targeting the sponsors of the World Cup," he said in a Skype conversation from an undisclosed location in Brazil. Asked to name the potential targets he mentioned Adidas, Emirates airline, the Coca-Cola Co and Budweiser.
Commodore said the hacker AnonManifest used a Trojan virus to get into the Foreign Ministry’s databases and steal the email accounts of several diplomats.
Subscribe to:
Posts
(
Atom
)